This is the sixth article in a series concerning the choice of architecture for your digital signage system, if you aren’t entirely clear on the notion of digital signage, or aren’t familiar with the different existing architectures, start by reading this article : Digital signage: preparing yourself well. If you’ve missed the last article, please read: Preparing yourself #5: Connectivity and bandwidth
In the age of connected watches and cars and the flourishing of cloud based solutions, the question of the security of these systems is a recurring problem. Digital signage is not spared of these considerations, and they are often at the heart of choices concerning which model to pick, most notably when the usage concerns internal communication. The security is a digital signage system, as everywhere, is first and foremost a question of compromises. Is the client ready to sacrifice features, speed of execution and comfort of use for more security?
The security in a digital signage system, as in any information system, is a complex notion, based on a trusting relationship with the service provider. It’s a subjective notion determined by the client company based on what they might see as the worst case scenario of an action d’une action attributable to a lack of “security”. In the case of digital signage, the principal preoccupations of a client company are in general the following:
- The image of the company, authenticity and coherence of displayed content.
- The confidentiality of data and content of the company.
- The integrity and inviolability of the companies’ information system .
Though the SaaS model is often accused of having issues with “security” and the (on premise) hosted one acclaimed, it is hard to formulate conclusions only on this basis, considering there are so many different implementations, each one comporting its own specificity. By focusing on the principal preoccupations, it is however possible to create a basis, but also to raise certain questions.
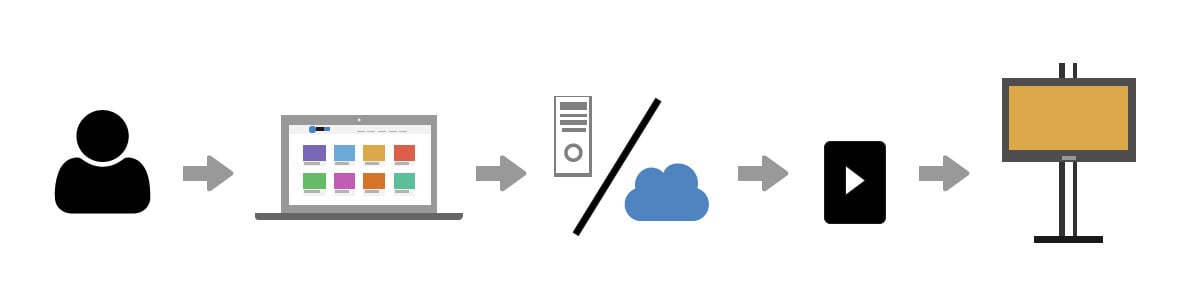
General information on digital signage
As a reminder, a digital signage system, reduced to its most simple use, can be summed up by the following case: A communicator wants to broadcast a message on a screen. This message exists in the form of a file (image, document or video). From his work post, he sends this file to the digital signage servers. At the moment of the broadcast, the server sends this file to the player responsible for the broadcast. The player reads the file and broadcasts the message. This case, though simple, requires the intervention of a number of pieces of equipment (and people), each one susceptible of presenting security risks in view of the companies’ preoccupations.
The image of the company
Digital signage is a communication tool. In this way, like all communication tools, it transmits messages that commit the company and contribute to its notoriety. These broadcasted messages represent the firm with the target audience. Thus, these messages have to be those (and only those) that the company decides to send out, without any change, accidental or intentional. Nevertheless, numerous changes can happen between the moment the communicator sends out content and the moment it is broadcasted on the display players. Though the use of a hosted (on premise) model suggests the elimination of this problem, it in truth reduces only its reach to a physical presence close to the company. In order to make sure that the content remains authentic and unchanged, the client would do good to check with his service provider (or to ask for the installation of) the following points:
The task of creating and broadcasting content, is it given to the same person?
Is the person charged with broadcasting the content trustworthy?
Does that person know the software well?
Is it the only person that can broadcast content?
Does the person share it’s identification with someone?
Is there a strong password policy in place for the management software (use of special characters, numbers, minimum length, frequent changing…) ?
Are the passwords kept on a post-it note?
Does the software implement a policy of Digital signatures ?
Are the files that are to be broadcasted signed ?
Are the software and systems used by the player trustworthy and up to date? Do they have vulnerabilities?
Are the screens physically accessible?
Is the remote control activated? In an extreme case, if the content where to be changed, is there a safety solution in place to stop the broadcast of this content? Will there be a trace of the author?
Thus, in the case of usage of a signature for the files, the threat can be found at the level of the display players, the management software (and the person or persons responsible for the broadcast). The choice of the model of the digital signage system can be seen as having little importance.

The confidentiality of data
Depending on the targets of the broadcasted messages, the content may necessitate heightened degrees of confidentiality. One need only think about broadcasts with important documents or strategic results whose publication could do harm to the company. Ensuring yourself that this content stays inside the company becomes a priority. However, for the digital signage system to work perfectly, it remains necessary to store the planned content on the server of the system (or at least to make it transit it). At first thought, the implementation of an (on premise) hosted model suggests a confinement of data on the internal network and thus a larger degree of protection of content, while a SaaS solution would suggest the contrary. In both cases, particular attention should be given to the trustworthiness of the management software, of the person using it, as well as the policy (and memorisation technique) concerning passwords. It is also important to make sure that the communications between the management software and the software are correctly cyphered, particularly in the case of a SaaS model, which uses the internet. It is also necessary to think about the storage of the data, and thus about the system server.
Is it situated in the client’s company ((on premise) hosted model) ?
If that is the case, is it accessible to anyone? Is it guarded at night? Is it situated in a datacentre (most SaaS models) ?
If that is the case, is the datacentre situated in a country that allows the collection of data?...
Lastly, it would be good to make sure that the communications between the server and the players are correctly cyphered and that the broadcast players aren’t subject to exploitable vulnerabilities.
Certain solutions implement a service for cyphering files that are to be broadcasted. These are cyphered beforehand, on the communicators post, stored in a cyphered form on the servers of the system, then sent to the players for broadcast, who are the only ones to be able to decipher the data before reading them. In this case, the physical protection of the players should also be ensured.

The integrity of the information system
The information system of a company has become the backbone of many enterprises. Numerous services that allow the company to survive and flourish rely on them. A digital signage system necessitates the installation of equipment that have to be able to communicate between them, often through a companies’ internal network. Furthermore, these players are rarely accessible by the client and constitute for them nothing but a black box that is hard to control. These black boxes can have problems with reliability or have vulnerabilities that could be exploited to penetrate the network of the company, in the case of a SaaS architecture, as well as an (on premise) hosted system. (With the latter, a physical proximity to the company remains necessary to exploit these vulnerabilities.
It would be good to give proper attention to the vulnerability of the broadcast players.
On what systems do they function and what services work on them?
Are they up to date? Do they have exploitable defaults?
Are they physically accessible? Is it possible to take control of one by connecting it to an external device?
In the case of SaaS models, it is often necessary to open ports in the firewall of the company to allow the players to get to the services of the service provider. In which case the vulnerabilities could be exploited from outside the company. In this case, the question of the reliability of the server becomes important again. If it is possible to take control over the server, then the secure communications between server and players as well as the means of securing the player would become ineffective. However, a precise, (and complex), configuration of the network equipment of the company can contribute to strongly diminishing the risks of intrusions and compromising the entire local network.
Nevertheless, the customer has the possibility of putting in place a local network, distinct from the ones used for its services, whether physically (different cables, different routers…), or virtually, by, for example, installing VLANs. The service provider can also put in place an alternative to using third party routers, like 3G/4G routers that connect the players to the internet without having to go through the internal network of the company.
Conclusion
Thus, notwithstanding that the preconceived notion that only an (on premise) hosted model offers “security” is hard to verify, it is true that this model allows you to implement satisfying security mechanisms in a simpler and less costly way. Though it is possible to reach equivalent degrees of security through a SaaS architecture, the solutions that have to be implemented are often more complex. Whatever the chosen architecture, it is always necessary to give particular attention to the global security policies and to identify the soft spots in advance, in order to prepare the security solutions, with the service provider, before the installation of the equipment. Other problems like the loss of data, the continuity of broadcasts, the availability of a management interface can also be a part of your preoccupations, in which case it would be imperative to identify them as early as possible in order to install the best possible solutions.
Read the following article Preparing yourself #7: Use and evolution.
You have a digital signage project, ask for a free demo.